US CISA adds ‘insane’ Linux Copy Fail flaw to watch list
Malicious actors with code execution capability may gain root access on Linux systems using as few as 10 lines of Python, according to a researcher.
A newly discovered vulnerability could affect most open-source major Linux distributions released since 2017, according to security researchers.
Codenamed “Copy Fail” by Xint.io and Theori, the flaw caught the attention of the US Cybersecurity and Infrastructure Agency (CISA), who added it to the Known Exploited Vulnerabilities (KEV) catalog on Saturday, warning it poses “significant risks to the federal enterprise.”
"An unprivileged local user can write four controlled bytes into the page cache of any readable file on a Linux system, and use that to gain root," the vulnerability research team at Xint.io and Theori said.
“10 lines of Python” may be all it takes: Researcher
The vulnerability can allow attackers to gain root access across a wide range of Linux systems using a 732-byte Python script, though it requires prior code execution on the system to escalate privileges.
Researcher Miguel Angel Duran said that it only requires “10 lines of Python” to access root permissions on any affected system.
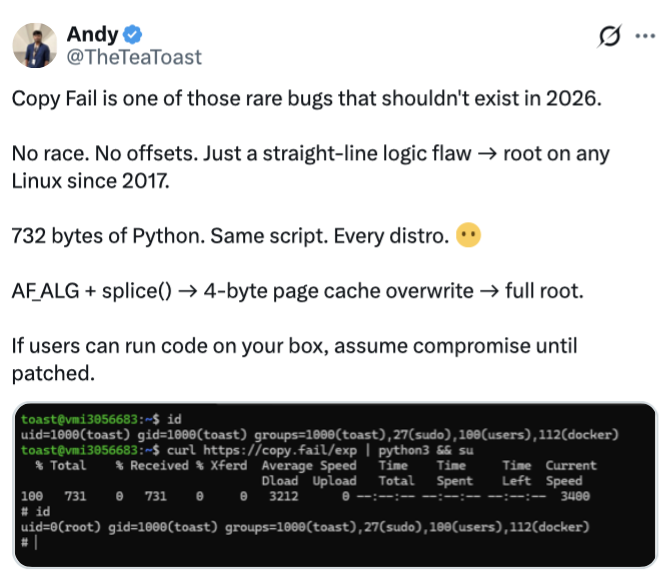
Source: Andy
“This Linux vulnerability is insane,” Duran said.
Linux is a widely used operating system by cryptocurrency exchanges, blockchain nodes and custodial services, due to its security and efficiency, meaning the vulnerability could potentially pose risks to the sector if attackers gain initial access.
Exploit was initially reported in March
Xint Code said in an X post on Saturday that the flaw “is a trivially exploitable logic bug in Linux, reachable on all major distros released in the last 9 years.”
“A small, portable python script gets root on all platforms,” Xint Code said.
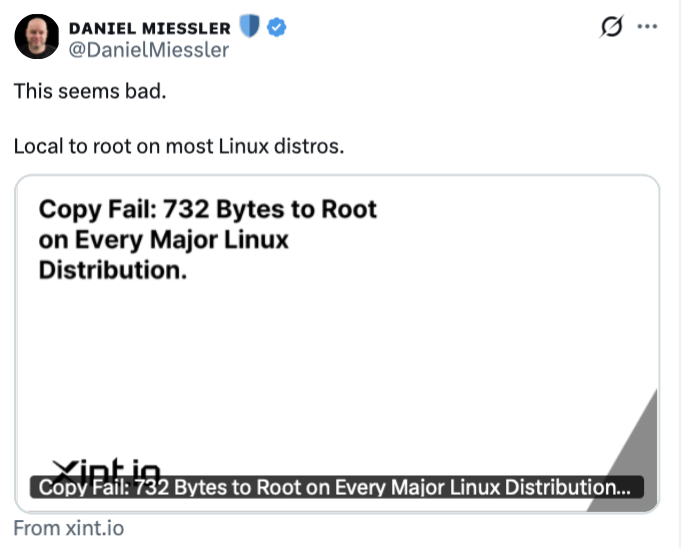
Source: Daniel Miessler
Cybersecurity firm Theori CEO Brian Pak said in an X post on Saturday that he reported the vulnerability “privately” to the Linux kernel security team on March 23.
“We worked with them on patches, which landed in mainline on April 1. CVE assigned April 22. We disclosed publicly on April 29 with a full write-up and PoC,” Pak said.
Discovery comes in wake of industry-wide "Project Glasswing" launch
The discovery of the flaw comes just as Project Glasswing is taking flight. The new initiative to secure what's described as "the world’s most critical software" brings together Amazon Web Services, Anthropic, Apple, Broadcom, Cisco, CrowdStrike, Google, JPMorganChase, the Linux Foundation, Microsoft, Nvidia and Palo Alto Networks.
In a launch announcement in early April, Anthropic said its Claude Mythos Preview frontier model showed that AI models have "reached a level of coding capability where they can surpass all but the most skilled humans at finding and exploiting software vulnerabilities."
"The fallout—for economies, public safety, and national security—could be severe. Project Glasswing is an urgent attempt to put these capabilities to work for defensive purposes," Anthropic said.
More on the subject