Litecoin gives post-attack update, as other devs doubt zero-day theory
Valid transactions that occurred during the affected blocks were not impacted and remain on the main chain, the Litecoin development team said.

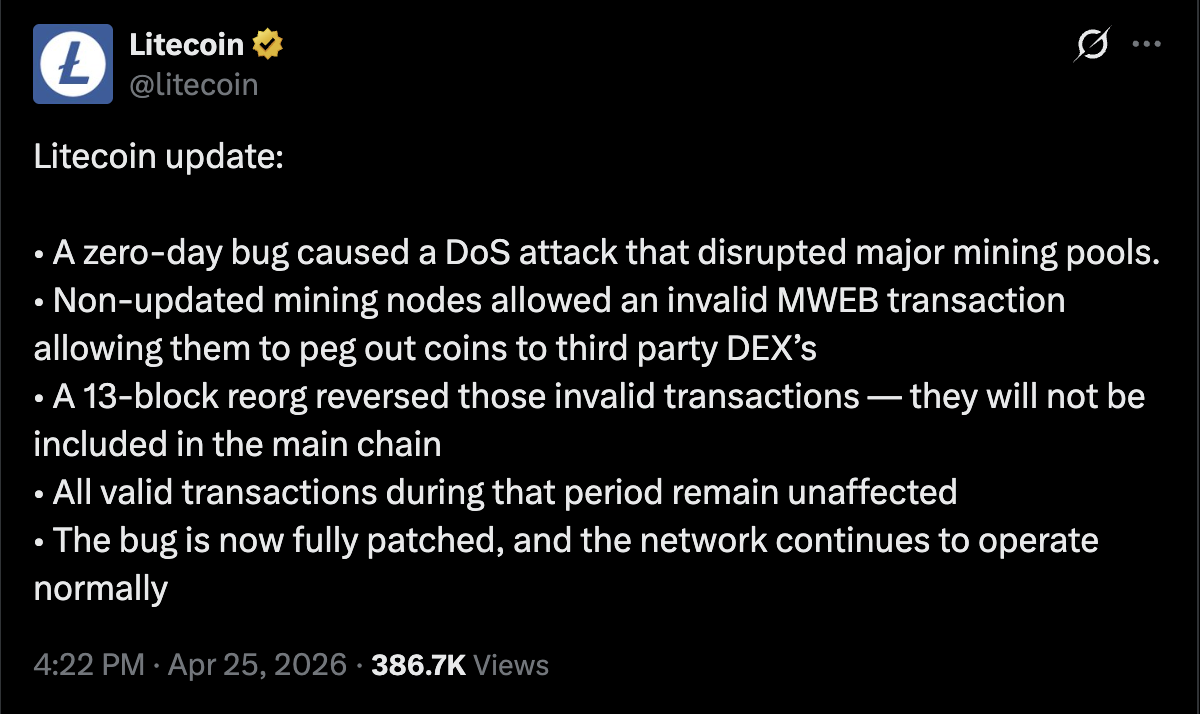
Litecoin, a layer-1 proof-of-work (PoW) blockchain network, was hit by a “zero-day” vulnerability on Saturday, which caused a 13-block reorganization of the chain, according to the Litecoin team, while other developers say the bug may have been previously known.
The bug caused a denial of service (DoS) attack on mining pools with newly updated software, suppressing their hashing power, according to an update from the Litecoin team.
This allowed older nodes to “peg out” coins to decentralized exchanges and cross-chain swap protocols, resulting in invalid transactions being posted to the network’s MimbleWimble Extension Blocks (MWEB) privacy layer, according to the team.
The updated nodes eventually regained control of the network’s hashing power, executing a 13-block reorganization that reversed the invalid transactions, which will not appear on the main chain. The bug has now been fully patched, the Litecoin team said.
Source: Litecoin on X
The incident comes amid an uptick in zero-day vulnerabilities -- that is, potential code exploits that are unknown to the software developers launching the product -- as AI systems like Anthropic’s Claude Mythos outperform human beings at identifying such attack surfaces.
Related: Kelp exploit highlights problem with non-isolated DeFi lending: Crypto execs
Some may have had advanced knowledge of software bug
A Binance address funded the attacker earlier in the week, suggesting that they had pre-planned the attack and had knowledge of the code exploit beforehand, according to Alex Shevchenko, co-founder of Aurora, a layer-2 scaling network. He said:
“The fact that protocol automatically handled the reorg once DoS stopped, which is great, means that some portion of the hashrate was actually running an updated code. Thus, this bug was known, and it's not a zero-day.”
“The timing and targeting suggest this wasn't a random opportunity,” blockchain developer Vadim said in response, adding, “Low hashrate layer 1’s are not safe collateral for cross-chain value anymore.”
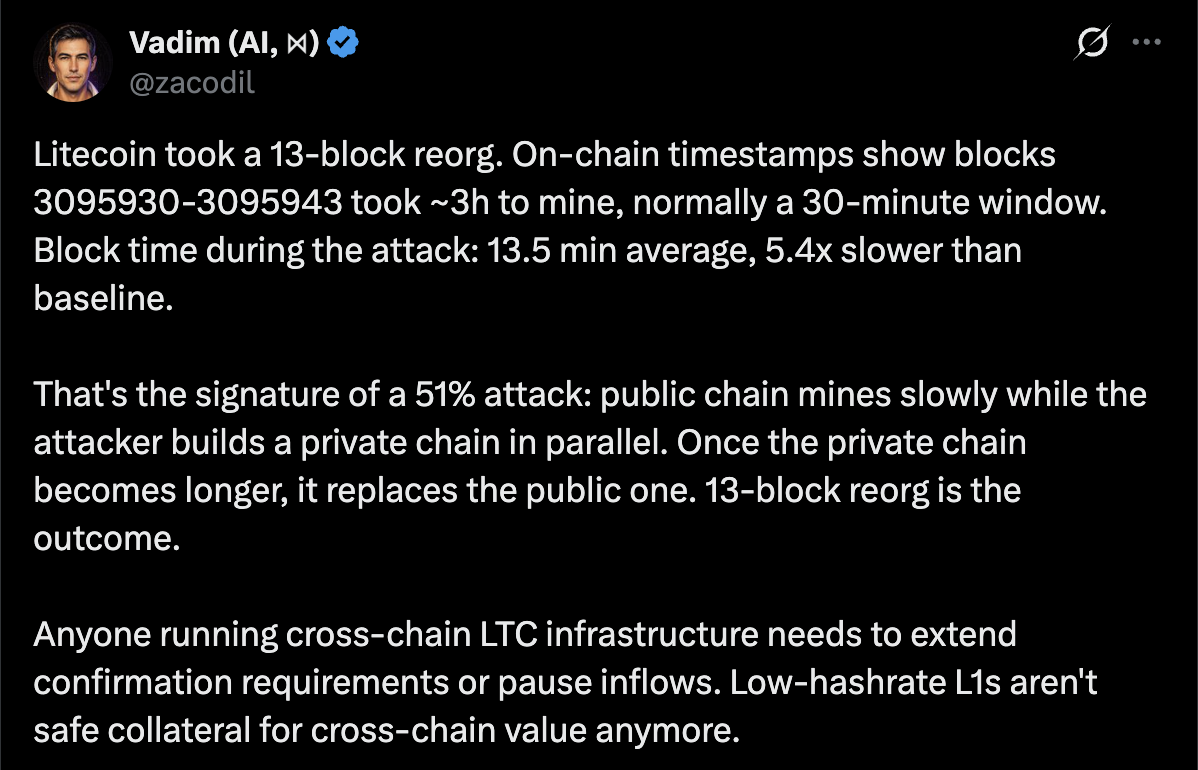
Source: Vadim (@zacodil on X)
Cross-chain bridges, which transfer digital assets between different blockchain protocols, have long been a major attack surface in crypto, causing billions of dollars in losses over the years.
The most recent high-profile example of a bridge exploit was the April 18 attack on the Kelp restaking protocol, which earlier this month left the platform drained of about $293 million.
Magazine: AI-driven hacks could kill DeFi — unless projects act now
More on the subject