AI is finding software bugs faster: Can crypto patch them fast enough?
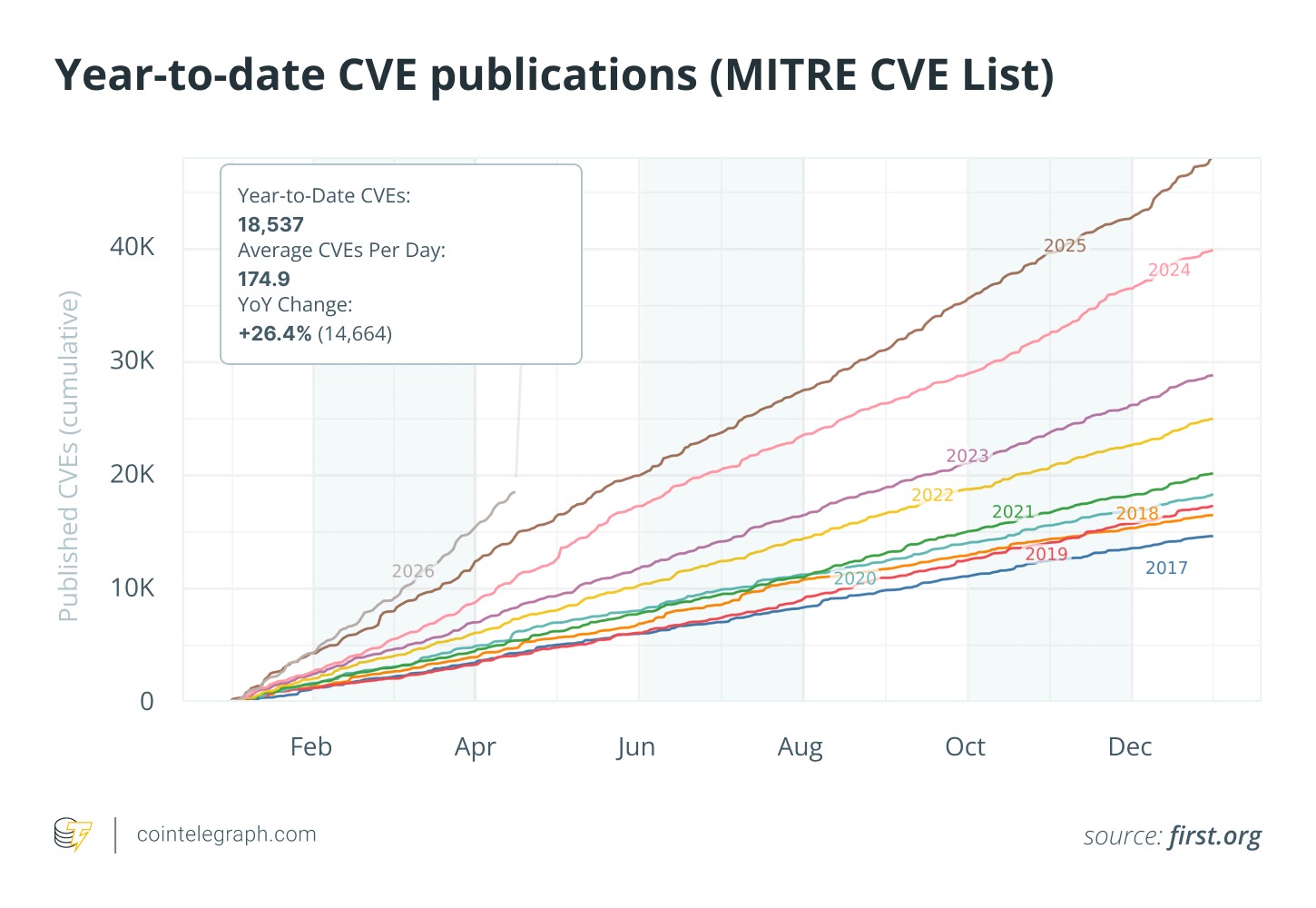
As AI speeds up CVE discovery, crypto exchanges, wallets and validators face growing pressure to identify vulnerable software and remediate risks quickly.
How AI is tightening crypto’s security timelines
Artificial intelligence is rapidly transforming cybersecurity, with major consequences for the cryptocurrency sector. Modern AI tools can help security teams identify software vulnerabilities faster.
These tools can handle automated code reviews and flag subtle flaws or risky patterns that manual reviews may miss. On the surface, this looks like a clear win for defense. Yet the picture is not entirely positive.
By speeding up vulnerability detection, AI can shorten the time organizations have to evaluate, prioritize and deploy fixes before bad actors take advantage. Crypto exchanges, wallets, validators and other critical infrastructure often rely on deeply interconnected open-source libraries, making this narrowing window a source of growing operational pressure across the sector.
The bigger concern is simpler: AI could leave crypto teams with much less time to fix software flaws after they are found. That would force the teams to move faster than ever when dealing with hidden flaws buried inside layered, complex software dependencies.
Why CVEs matter for crypto security
A CVE (Common Vulnerabilities and Exposures) is a standardized, publicly assigned identifier for a specific software flaw. It is overseen by the MITRE CVE Program and cataloged in resources such as the National Vulnerability Database (NVD).
These IDs create a common language that security professionals, developers and companies can use to refer to the exact same issue. For instance, when a bug is found in widely used tools such as OpenSSL, SQLite or certain Linux kernel modules, it may be labeled something like CVE-2025-7123. This unique tag allows teams to quickly reference key details such as:
- How serious the vulnerability is
- Which versions are affected
- Available fixes or workarounds
- Evidence of active exploitation
- Recommended steps to reduce risk
A CVE is not a solution. It is simply a label that flags the existence of a problem. The real work still falls on organizations to check whether they are using the affected component, then apply patches or other protections promptly.
In the cryptocurrency sector, this process is often more challenging. Many crypto platforms are built on complex stacks of open-source components that are not always fully inventoried or monitored.
How AI is changing the CVE lifecycle
In the past, finding and addressing vulnerabilities moved at a slower, more measured pace. Researchers identified issues, vendors studied them, patches were created and organizations gradually deployed updates over days or even weeks.
AI tools are now making this process much faster. In 2025, Google’s AI system, known as “Big Sleep,” played a key role in discovering a vulnerability in SQLite with real-world exploit potential. Around the same time, Microsoft highlighted how AI-assisted techniques helped uncover vulnerabilities in popular open-source bootloaders such as GRUB2 and U-Boot.
These examples show that AI can help security teams scan massive code repositories faster and detect risky patterns that might otherwise go unnoticed for longer.
However, this acceleration works in both directions. Once a vulnerability is publicly disclosed, malicious actors can also use automated tools and AI to analyze and weaponize it more rapidly. While not every CVE will trigger immediate attacks, the overall window for organizations to assess their risk and implement defenses is getting narrower.
For cryptocurrency companies managing always-on infrastructure and large asset values, even minor delays in response can carry outsized consequences.
Did you know? The famous Heartbleed vulnerability from 2014 affected OpenSSL, a widely used cryptographic library across the internet. It also affected parts of the crypto ecosystem at the time, including Bitcoin Core, some Bitcoin clients, wallets and exchanges.
Why CVEs matter to crypto
A common assumption is that crypto security revolves mainly around blockchain consensus mechanisms and advanced cryptography. However, crypto platforms depend on the same software components used across the broader tech industry.
Common dependencies in crypto infrastructure include:
- Linux-based operating systems
- OpenSSL and other cryptographic libraries
- SQLite and other database engines
- Container technologies such as Docker
- Cloud services and APIs
- Web servers and frameworks
- Programming language ecosystems such as Node.js, Python, Go and Rust
- Logging, monitoring and authentication tools
A single exchange may operate hundreds or thousands of interconnected services, while wallets often rely on mobile SDKs, browser extensions and third-party libraries. Node operators and validators use networking protocols, OS kernels and database systems daily.
A vulnerability in a seemingly routine software package can ripple through crypto operations, even if the underlying blockchain or cryptographic primitives remain untouched. This layered reality explains why CVEs are becoming increasingly important for the cryptocurrency sector.
The core challenge: Limited visibility into what crypto teams actually run
A key hurdle in fixing vulnerabilities is simply knowing where they exist within an organization’s environment. When a new CVE is published, the first question security and engineering teams must answer is basic:
“Are we even using this vulnerable component?”
Answering that question is often more difficult than it seems. Modern applications are built on layers of external dependencies, including code libraries pulled in from third parties. Many of these are transitive dependencies, meaning they are brought in automatically by other packages rather than directly chosen by developers.
Because of this, vulnerable code can quietly sit inside:
- Container images
- Internal tooling and scripts
- Validator and node infrastructure
- Build pipelines
- Back-end APIs
- Wallet applications
- Developer workstations
- Testing and staging environments
In many cases, the real difficulty is not applying a patch. It is first discovering that you are exposed.
This issue becomes more serious in cryptocurrency operations, where infrastructure evolves quickly, incorporates numerous open-source projects and runs across decentralized and cloud-based setups.
Did you know? A single vulnerable open-source package can indirectly affect thousands of downstream packages, projects and applications because modern software often relies on deeply nested dependencies.
How complex software supply chains create hidden risks
Over the past decade, software supply chains have grown increasingly complex. A typical application can depend on hundreds or even thousands of external packages, many of which are maintained by independent developers around the world.
This complexity creates blind spots. A vulnerable library can enter a crypto system through various routes, such as:
- Pre-built cloud images or virtual machines
- Automatic dependency updates
- Outdated or unmaintained open-source projects
- Third-party plug-ins or extensions
- Forked code repositories
- Base layers in container environments
Even mature organizations can struggle to maintain a complete, real-time map of every dependency relationship.
This is why supply-chain attacks have become more prominent. Rather than targeting individual companies directly, attackers often compromise popular shared components, potentially affecting thousands of downstream users at the same time. Crypto projects and companies are just as vulnerable to these indirect threats.
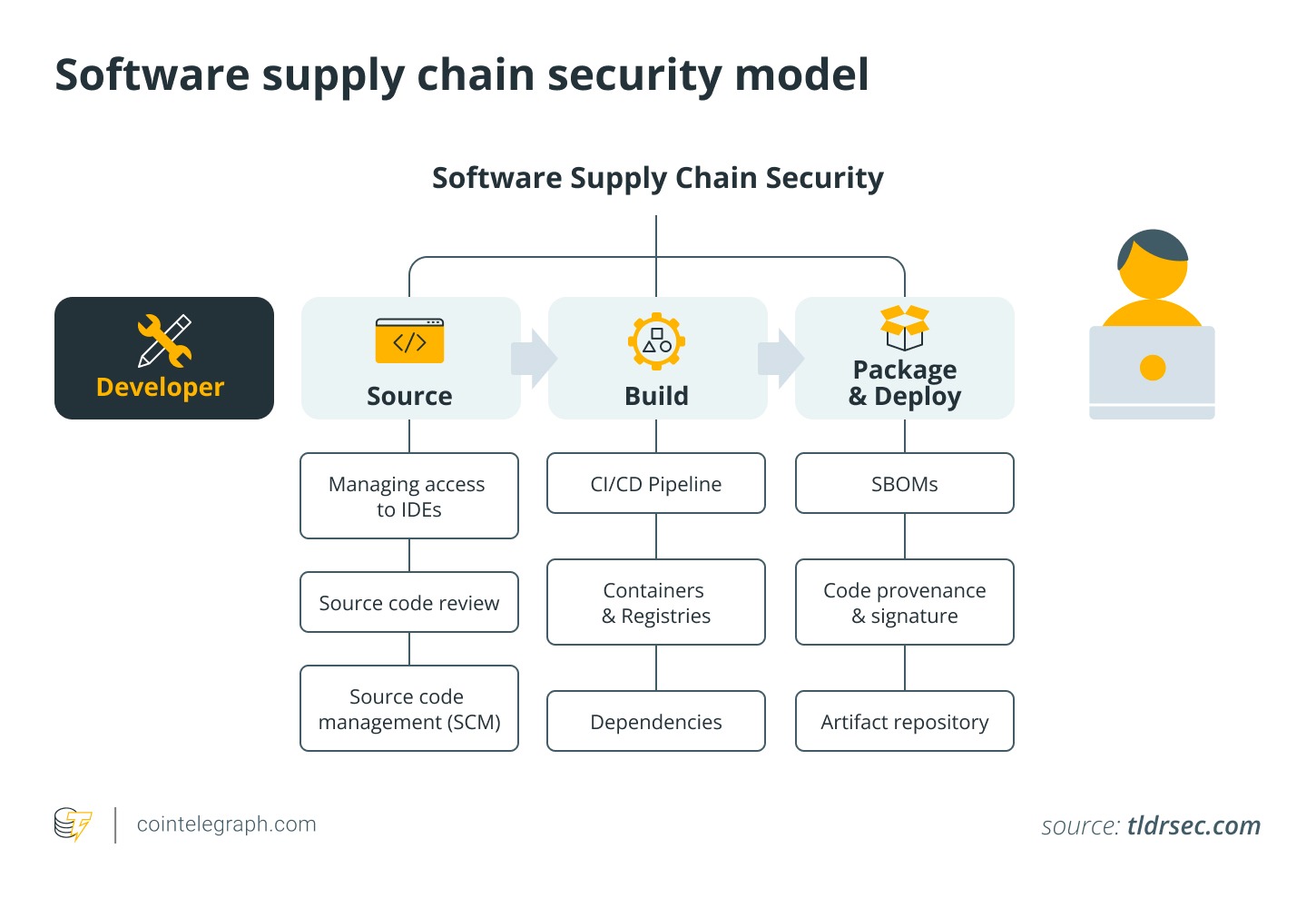
What an SBOM is and why it helps
To tackle these visibility gaps, security professionals recommend adopting SBOMs (Software Bills of Materials). An SBOM is a detailed inventory, or “ingredients list,” for software.
An SBOM catalogs the components, libraries and dependencies used in an application or system, ideally including both direct and transitive dependencies. A well-maintained SBOM typically records:
- Component names and identifiers
- Exact version numbers
- Original suppliers or maintainers
- How components relate to one another, such as dependency trees
- Unique tracking IDs, such as package-URL references
- Creation timestamps
The goal is simple. When a new vulnerability surfaces, teams can quickly check whether it affects them, which systems are involved and what needs urgent attention.
Without an SBOM, engineers may spend hours or days manually searching through codebases and environments. With an up-to-date SBOM, teams can determine exposure levels, prioritize fixes and respond much faster.
For cryptocurrency infrastructure, where systems often run continuously and handle significant asset value, this kind of visibility can strengthen security and reduce risk.
Did you know? Some crypto exchanges run infrastructure containing millions of lines of code, much of which comes from standard open-source software rather than blockchain code itself.
Why different crypto components face unique CVE risks
Not every part of the cryptocurrency ecosystem is exposed to vulnerabilities in the same way. Each major element, including nodes, validators, wallets and exchanges, carries its own risk profile.
- Nodes: Blockchain nodes often depend on networking stacks, remote procedure call (RPC) endpoints, operating systems and database layers. A vulnerability in any of these areas can affect node availability, block synchronization or expose remote access points to potential abuse.
- Validators: Validators operate under constant pressure to maintain strong security and maximum uptime. In proof-of-stake networks, urgent patching may require restarts or scheduled downtime, which can lead to missed blocks, missed rewards, inactivity penalties or, on some networks, downtime-related slashing depending on protocol rules.
- Wallets: Wallet applications are particularly sensitive because they interact directly with users. Risks often stem from browser-based environments, dependency libraries or key-signing processes.
- Exchanges: Exchanges typically present one of the broadest attack surfaces in the industry. Their complex setups include trading engines, hot wallets, public APIs, databases, cloud platforms, monitoring systems and internal admin tools. Any delay in addressing vulnerabilities can quickly lead to financial losses, operational disruptions and reputational damage.
How delayed remediation affects crypto users
Slow responses to vulnerabilities do not always result in stolen assets, but they can increase overall risk and lead to:
- Unexpected service downtime or degraded performance
- Temporary halts on deposits or withdrawals
- Increased risk of wallet or account breaches
- Broader network or infrastructure instability
- Heightened regulatory attention
- Erosion of user trust and platform reputation
The real-world danger of any given CVE depends on multiple variables, including:
- Whether the vulnerable code path is actively used
- Whether the affected system is exposed to the internet
- Availability of public exploit code
- Realistic attacker access to the environment
- Existence of effective temporary mitigations
Some vulnerabilities look alarming on paper but prove hard to weaponize in practice. Others can escalate rapidly when they target commonly used, externally facing services.
The central issue remains speed combined with smart prioritization.
Did you know? SBOMs are often compared to ingredient labels on food packaging because they help organizations see exactly which components exist inside software.
Building a faster, more effective CVE remediation process
With AI speeding up vulnerability discovery, crypto organizations should focus on strengthening their overall response processes instead of blindly rushing patches.
A robust remediation strategy typically involves:
- Keeping comprehensive inventories of all software assets
- Regularly generating and updating SBOMs
- Mapping full dependency trees across environments
- Prioritizing fixes based on actual exploit likelihood and system exposure
- Thoroughly testing patches in staging before live deployment
- Using controlled, phased rollout procedures
- Conducting post-remediation verification and monitoring
The objective is to avoid reactive, panic-driven updates every time a new vulnerability makes headlines. Instead, teams need reliable, rapid methods to determine genuine exposure and act only where it truly matters.
This visibility-first mindset will become even more essential as vulnerability disclosure cycles continue to accelerate.
Using SBOMs to strengthen crypto security
SBOMs are a strong starting point, but they become far more useful when paired with additional tools:
- Dependency graphs: These create a clear visual overview of how different software components connect across an organization’s systems. They highlight hidden, indirect risks that may not appear in a basic component list.
- Reproducible environments: These go a step further by ensuring that the same versions of libraries and packages are used across development, testing and live production setups. This reduces version mismatches that often complicate emergency responses.
Together, these approaches reduce confusion when vulnerabilities surface under pressure. Teams spend less time asking, “Do we even have this anywhere?” and can instead focus on the more important question: “How do we contain and resolve this risk quickly and safely?”
What everyday crypto users need to know
Individual users also contribute meaningfully to overall ecosystem safety. Helpful habits include:
- Regularly updating wallets, apps and extensions
- Sourcing software only from verified official websites or stores
- Watching out for phishing scams that pretend to offer urgent security fixes
- Storing larger amounts in hardware wallets for better protection
- Paying attention to trusted project announcements during major vulnerability disclosures
Crucially, users should not panic at every new CVE report. Headlines can sound alarming, but real-world exploit risk differs greatly depending on the specifics. Many issues remain theoretical or limited in scope.
That said, consistent software maintenance across the board helps build a more resilient environment and supports greater confidence in crypto platforms.
The real risk is slow patching, not AI-detected bugs
AI-assisted vulnerability detection does not mean major breaches are unavoidable or imminent. Several important points need to be considered:
- AI tools strengthen defensive capabilities, even as they may also aid attackers
- Most CVEs never see real-world exploitation
- Many flaws affect only very specific or uncommon setups
- Fixes and temporary protections are often released shortly after disclosure
- Better visibility tools help teams respond more effectively and efficiently
The fundamental change is operational. As AI speeds up discovery, analysis and public disclosure, crypto organizations will face tighter response timelines.
This shift highlights the growing importance of deep, accurate insight into software supply chains. It moves the focus away from last-minute scrambling and toward calm, well-informed action.
More on the subject

