MediaTek patches bug enabling crypto seed theft in just 45 seconds
Ledger’s white-hat security team said it found a flaw in MediaTek's secure boot chain that can be used to steal sensitive information from certain Android devices.

Update (March 19 at 11:51 am UTC): This article has been updated to include comments from a Trustonic spokesperson.
Update (March 26 at 1:00 am UTC): This article has been updated to include a response from Ledger chief technology officer Charles Guillemet.
Mobile phone chipmaker MediaTek patched a vulnerability affecting its chipsets in January that could have allowed an attacker to steal crypto seed phrases on affected devices using just a USB cable and the right software.
The flaw was discovered by Ledger’s white-hat security team, Donjon, who had shared the vulnerability with MediaTek before a patch was rolled out on Jan. 5, though users who have not installed the latest security patches are advised to do so, said Ledger.
Test device compromised in 45 seconds
In a statement shared with Cointelegraph, Ledger explained that the flaw meant an attacker with access to an Android phone could connect it to a computer via USB and bypass security protections, potentially gaining access to sensitive data on the device, including crypto wallet seed phrases.
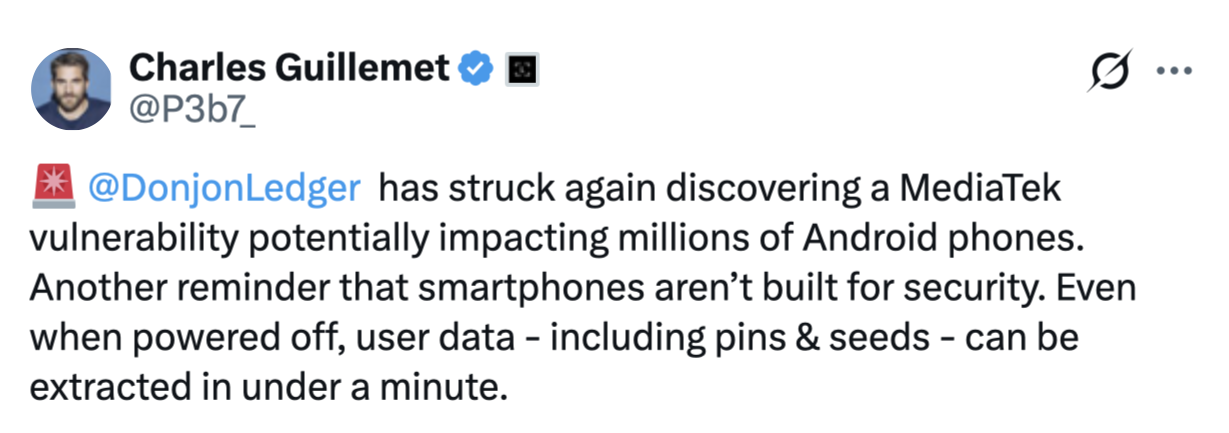
Source: Charles Guillemet
Donjon demonstrated the hack by connecting a Nothing CMF Phone 1 to a laptop and compromising the device’s security in approximately 45 seconds.
“Without ever even booting into Android, the exploit automatically recovered the phone’s PIN, decrypted its storage, and extracted the seed phrases from the most popular software wallets: Trust Wallet, Base, Kraken Wallet, Rabby, Tangem’s Mobile Wallet and Phantom,” Ledger said.
While Ledger suggested the vulnerability has the potential to affect Android smartphones using Trustonic’s Trusted Execution Environment (TEE) and MediaTek processors, Trustonic said the issue did not come from its software.
“The issue highlighted here by Ledger could potentially impact any software using the seed for security provided by MediaTek’s secure boot flow,” a spokesperson told Cointelegraph.
“Trustonic is not on all MediaTek chipsets hence calling out Trustonic explicitly is not reasonable,” they added.
Ledger chief technology officer Charles Guillemet responded: “The vulnerability that was found is at the SoC level (Mediatek), and in this case the TEE running on it does not protect the Android KeyStore. This is what was demonstrated with Trustonic, which is present on many Mediatek phones."
MediaTek’s secure boot chain is a security mechanism built into its chips that ensures a phone starts safely and only with authorized software during startup.
Ledger has urged users to update their devices, though a Ledger spokesperson told Cointelegraph they “don’t anticipate this to be an ongoing issue.”
Mobile phones are never safe, Ledger says
With almost 36 million people managing digital assets on their phones as of early 2025, even a single vulnerability could put a significant number of wallets at risk.
In December 2025, Ledger revealed that it tested an attack on the MediaTek Dimensity 7300 (MT6878), and bypassed its security measures to gain “full and absolute control over the smartphone, with no security barrier left standing.”
Guillemet told Cointelegraph in June 2020 that mobile phones, whether Android or iPhone, are “very difficult to have secure applications.”
Related: SlowMist introduces Web3 security stack for autonomous AI agents
He reinforced a similar view on Wednesday, posting on X: “Smartphones aren’t built for security. Even when powered off, user data - including pins & seeds - can be extracted in under a minute.”
“This research highlights a fundamental architectural difference: General-purpose chips are built for convenience. Secure Elements are built for key protection. A dedicated Secure Element isolates secrets from the rest of the system, protecting them even under physical attack,” he said.
Magazine: All 21 million Bitcoin is at risk from quantum computers
More on the subject

